RemoteIoT Platform SSH Download for Mac has become an essential tool for developers and IT professionals who need secure access to their IoT devices from anywhere. Whether you're working remotely or managing multiple devices across different locations, understanding how to use SSH on a Mac can significantly enhance your productivity and security.
In today's interconnected world, the Internet of Things (IoT) is expanding rapidly, and with it comes the need for secure, efficient communication between devices. RemoteIoT Platform offers a robust solution for managing IoT devices remotely, and downloading SSH on a Mac allows users to access these devices securely.
This article will explore the RemoteIoT Platform, its SSH capabilities, and provide a step-by-step guide for downloading and configuring SSH on a Mac. We'll also cover best practices, troubleshooting tips, and frequently asked questions to ensure you have all the information you need to get started.
Read also:Isabel May A Rising Star In The Entertainment Industry
Table of Contents
- Introduction to RemoteIoT Platform
- Understanding SSH and Its Importance
- Overview of RemoteIoT Platform
- Setting Up SSH on a Mac
- How to Download SSH for Mac
- Configuring SSH for RemoteIoT
- Best Practices for Using SSH
- Common Issues and Troubleshooting
- Enhancing Security with SSH
- Conclusion and Next Steps
Introduction to RemoteIoT Platform
RemoteIoT Platform is a cutting-edge solution designed to simplify the management of IoT devices. It provides a secure and efficient way to connect to devices remotely, making it an ideal choice for developers, IT professionals, and businesses alike.
The platform supports various protocols, including SSH, which ensures secure communication between devices. By leveraging SSH, users can access their IoT devices from anywhere, ensuring seamless operation and maintenance.
With the growing demand for remote work and device management, understanding how to use SSH on a Mac is crucial. This guide will walk you through the process of downloading and configuring SSH for RemoteIoT Platform.
Understanding SSH and Its Importance
SSH, or Secure Shell, is a cryptographic network protocol that enables secure communication between devices over an unsecured network. It is widely used for remote login and command execution, making it indispensable for managing IoT devices.
Why Use SSH?
- Enhanced security through encryption
- Reliable authentication mechanisms
- Support for various commands and file transfers
SSH is particularly important for RemoteIoT Platform users who need to manage devices remotely. By encrypting data transmissions, SSH ensures that sensitive information remains protected from unauthorized access.
Read also:Who Is David Muirs Wife Exploring The Life Of Melanie Cole
Overview of RemoteIoT Platform
RemoteIoT Platform is designed to address the challenges of managing IoT devices in a secure and efficient manner. It offers a range of features that make it an ideal choice for businesses and individuals alike.
Key Features
- Secure device connectivity
- Centralized management dashboard
- Support for multiple protocols, including SSH
- Scalability for growing IoT ecosystems
By integrating SSH into its platform, RemoteIoT ensures that users can access their devices securely, regardless of location. This makes it an essential tool for anyone working with IoT devices.
Setting Up SSH on a Mac
MacOS comes with built-in support for SSH, making it easy to set up and use. Here's a step-by-step guide to help you get started:
Step 1: Enable SSH on Your Mac
To enable SSH on your Mac, follow these steps:
- Open System Preferences
- Select Sharing
- Check the box for Remote Login
Step 2: Verify SSH Installation
MacOS includes SSH by default. To verify its installation, open the Terminal app and type:
ssh -V
This command will display the version of SSH installed on your Mac.
How to Download SSH for Mac
In most cases, SSH is already installed on your Mac. However, if you need additional tools or a specific version, you can download them from trusted sources such as OpenSSH.
Alternative Tools
- Homebrew: A popular package manager for MacOS that simplifies the installation of additional SSH tools.
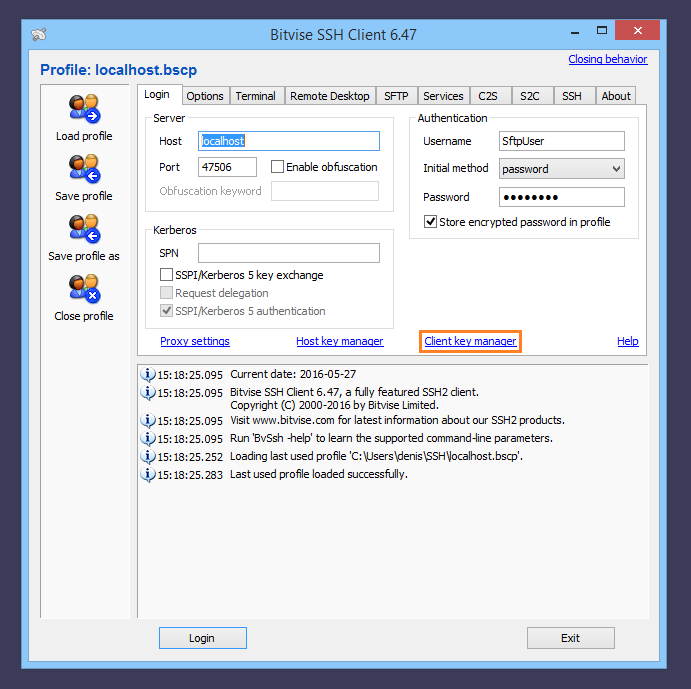
- Third-party clients: Applications like PuTTY (for Windows) or MobaXterm offer advanced features for SSH users.
When downloading SSH tools, always ensure you are using a reputable source to avoid security risks.
Configuring SSH for RemoteIoT
Once SSH is installed and enabled on your Mac, you can configure it to work with RemoteIoT Platform. Here's how:
Step 1: Generate SSH Keys
SSH keys provide a secure way to authenticate your connection. To generate keys:
- Open Terminal
- Type:
ssh-keygen -t rsa -b 4096 -C "your_email@example.com" - Follow the prompts to save the key and set a passphrase
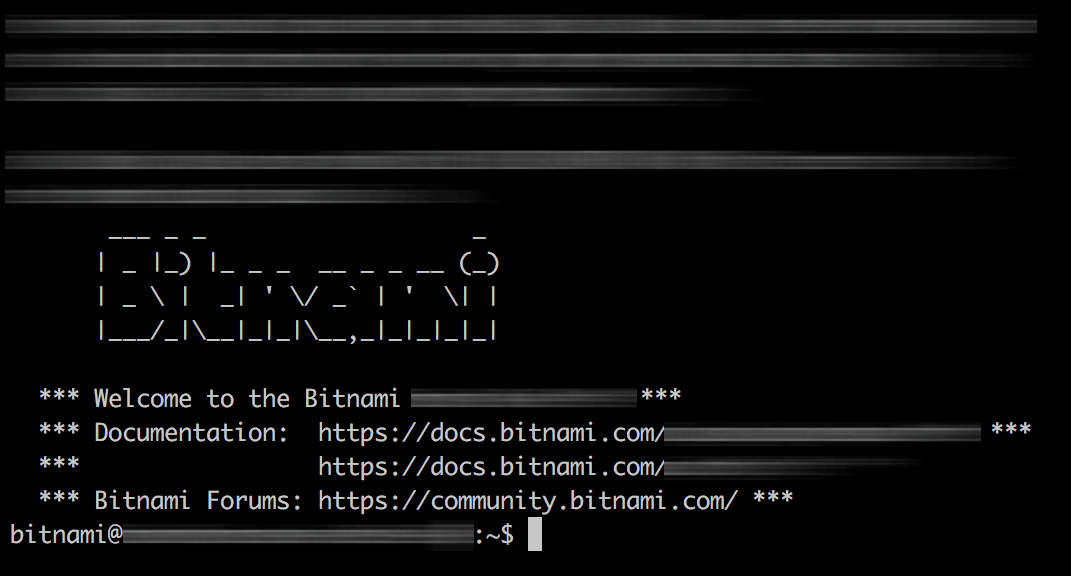
Step 2: Connect to RemoteIoT Devices
To connect to a RemoteIoT device, use the following command:
ssh username@remote_device_ip
Replace "username" and "remote_device_ip" with the appropriate values for your setup.
Best Practices for Using SSH
Using SSH effectively requires adherence to best practices to ensure security and efficiency. Here are some tips:
1. Use Strong Passwords and Passphrases
Strong authentication mechanisms are crucial for protecting your SSH connections. Use complex passwords and passphrases to enhance security.
2. Regularly Update SSH
Keeping your SSH software up to date helps protect against vulnerabilities. Regularly check for updates and apply them promptly.
3. Monitor Access Logs
Regularly reviewing access logs can help identify unauthorized access attempts and potential security threats.
Common Issues and Troubleshooting
While SSH is generally reliable, issues can arise. Here are some common problems and their solutions:
Problem: Connection Refused
Solution: Ensure that the SSH service is running on the remote device and that the IP address and port number are correct.
Problem: Permission Denied
Solution: Verify that the SSH keys are correctly configured and that the user has the necessary permissions to access the device.
Enhancing Security with SSH
SSH offers several features to enhance security:
1. Use Key-Based Authentication
Key-based authentication eliminates the need for passwords, reducing the risk of brute-force attacks.
2. Disable Root Login
Disabling root login prevents unauthorized users from gaining administrative access to your devices.
3. Limit Access to Specific IPs
Restricting access to specific IP addresses can further enhance security by limiting who can connect to your devices.
Conclusion and Next Steps
RemoteIoT Platform SSH download for Mac is a powerful tool for managing IoT devices securely and efficiently. By following the steps outlined in this guide, you can set up and configure SSH on your Mac to work seamlessly with RemoteIoT Platform.
Remember to adhere to best practices and regularly update your SSH software to ensure maximum security. For more information, visit the official OpenSSH website or consult the RemoteIoT Platform documentation.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more tips and insights on IoT and secure communication.