As the Internet of Things (IoT) continues to expand, the need for secure remote access to IoT devices has never been more critical. Best remote IoT device SSH solutions are essential for maintaining secure connections, ensuring data privacy, and enabling seamless device management. In this article, we will explore the best remote IoT device SSH options, their features, and how they can enhance your IoT infrastructure.
IoT devices are transforming industries by enabling smarter, more connected systems. However, these devices often require remote access for configuration, troubleshooting, and maintenance. Without proper security measures, unauthorized access can lead to data breaches and system vulnerabilities. This is where SSH (Secure Shell) comes into play, offering encrypted communication channels to protect your IoT ecosystem.
In this comprehensive guide, we will delve into the top remote IoT device SSH solutions, discuss their benefits, and provide actionable insights to help you choose the right tool for your needs. Whether you're a developer, IT professional, or business owner, this article will equip you with the knowledge to secure your IoT devices effectively.
Read also:Nick Gilder Partner The Untold Story And Insights
Table of Contents
- Introduction to Remote IoT Device SSH
- Understanding SSH Basics
- Why SSH is Important for IoT Devices
- Best Remote IoT Device SSH Solutions
- Enhancing Security with SSH
- How to Set Up SSH for IoT Devices
- Benefits of Using SSH for IoT Devices
- Common Challenges and Solutions
- The Future of Remote IoT Device SSH
- Conclusion and Call to Action
Introduction to Remote IoT Device SSH
IoT devices are increasingly being deployed in various industries, from smart homes to industrial automation. These devices often require remote management, making secure access critical. Best remote IoT device SSH solutions provide encrypted communication channels, ensuring data integrity and privacy. This section will introduce the concept of SSH and its role in securing IoT devices.
SSH, or Secure Shell, is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. It is widely used for remote command-line login and data transfer, offering robust encryption and authentication mechanisms. For IoT devices, SSH ensures that sensitive data remains protected from unauthorized access and cyber threats.
By leveraging SSH, organizations can manage their IoT devices remotely without compromising security. This is particularly important for devices deployed in remote locations or those requiring frequent updates and maintenance. Understanding the basics of SSH is the first step toward securing your IoT infrastructure.
Understanding SSH Basics
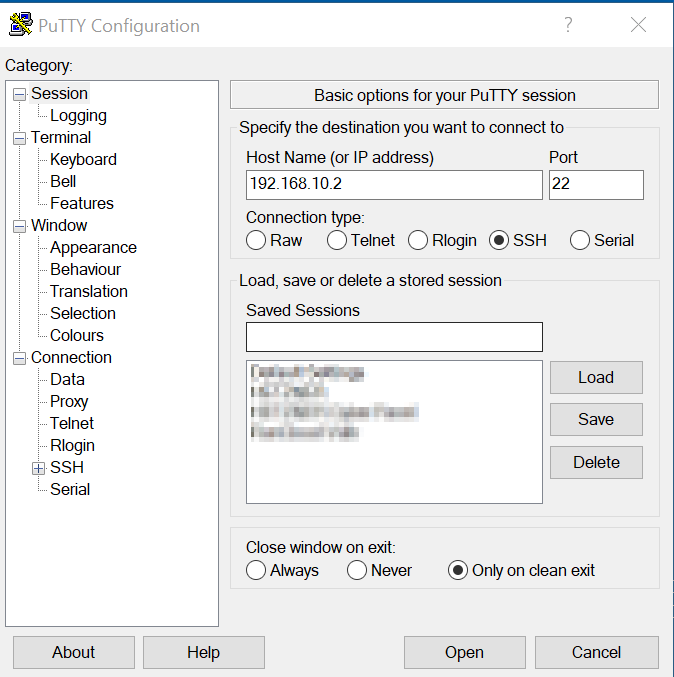
Before diving into the best remote IoT device SSH solutions, it is essential to understand the fundamentals of SSH. SSH operates on port 22 by default and uses public-key cryptography for authentication. It supports various encryption algorithms, including AES and ChaCha20, ensuring secure data transmission.
Key features of SSH include:
- Encryption: SSH encrypts all data transmitted between devices, preventing eavesdropping and data tampering.
- Authentication: SSH supports multiple authentication methods, including password-based and public-key authentication.
- Portability: SSH can be used across different platforms and operating systems, making it versatile for IoT devices.
For IoT devices, SSH provides a secure and reliable method for remote access, enabling administrators to manage devices from anywhere in the world. Understanding these basics will help you make informed decisions when selecting an SSH solution for your IoT infrastructure.
Read also:Lucy Chen Actress Rising Star In The Entertainment Industry
Why SSH is Important for IoT Devices
IoT devices often operate in unsecured environments, making them vulnerable to cyberattacks. Without proper security measures, unauthorized access can lead to data breaches, system downtime, and financial losses. SSH plays a crucial role in securing IoT devices by providing encrypted communication channels and robust authentication mechanisms.
Key reasons why SSH is important for IoT devices include:
- Data Privacy: SSH ensures that sensitive data transmitted between devices remains private and secure.
- Device Management: SSH enables secure remote access for device configuration, troubleshooting, and maintenance.
- Cybersecurity: SSH protects IoT devices from unauthorized access and cyber threats, enhancing overall system security.
By implementing SSH for IoT devices, organizations can safeguard their infrastructure and ensure seamless operations. This section highlights the importance of SSH in the context of IoT and its impact on security and efficiency.
Best Remote IoT Device SSH Solutions
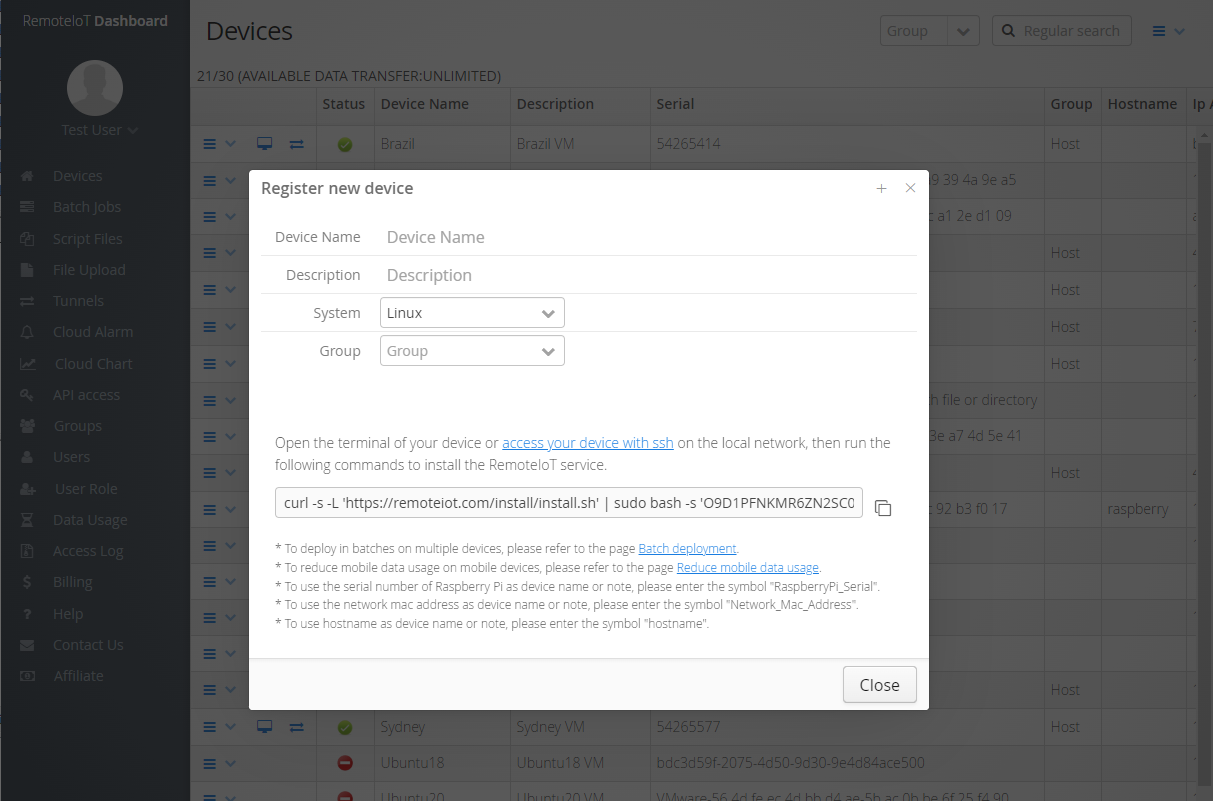
There are several SSH solutions available for remote IoT device management. Each solution offers unique features and benefits, catering to different use cases and requirements. In this section, we will explore the top remote IoT device SSH solutions and their capabilities.
Solution 1: OpenSSH
OpenSSH is one of the most widely used SSH solutions, known for its open-source nature and robust security features. It supports a wide range of encryption algorithms and authentication methods, making it ideal for IoT devices. Key features of OpenSSH include:
- Open Source: OpenSSH is free to use and modify, allowing developers to customize it for their specific needs.
- Compatibility: OpenSSH supports multiple platforms, including Linux, Windows, and macOS, ensuring seamless integration with IoT devices.
- Security: OpenSSH provides strong encryption and authentication mechanisms, protecting IoT devices from unauthorized access.
OpenSSH is a reliable choice for organizations seeking a secure and flexible SSH solution for their IoT infrastructure.
Solution 2: Bitvise SSH
Bitvise SSH is a commercial SSH solution that offers advanced security features and ease of use. It is particularly well-suited for enterprise environments, providing robust protection for IoT devices. Key features of Bitvise SSH include:
- Enterprise-Grade Security: Bitvise SSH offers advanced encryption and authentication options, ensuring maximum security for IoT devices.
- User-Friendly Interface: Bitvise SSH provides an intuitive interface, making it easy for administrators to manage IoT devices remotely.
- Support: Bitvise SSH offers comprehensive support and documentation, helping users troubleshoot issues and optimize performance.
Bitvise SSH is an excellent choice for organizations requiring enterprise-grade security and ease of use for their IoT devices.
Solution 3: Dropbear SSH
Dropbear SSH is a lightweight SSH solution designed for resource-constrained environments, such as embedded IoT devices. It offers a minimal footprint while maintaining strong security features. Key features of Dropbear SSH include:
- Lightweight: Dropbear SSH is optimized for low-resource environments, making it ideal for embedded IoT devices.
- Security: Dropbear SSH supports strong encryption and authentication mechanisms, ensuring secure communication for IoT devices.
- Flexibility: Dropbear SSH can be easily integrated into various IoT platforms, providing flexibility for developers.
Dropbear SSH is a great choice for organizations deploying IoT devices with limited resources, offering a balance between security and performance.
Enhancing Security with SSH
While SSH provides robust security features, additional measures can further enhance the protection of IoT devices. These include:
- Key-Based Authentication: Using key-based authentication instead of passwords reduces the risk of brute-force attacks.
- Firewall Configuration: Configuring firewalls to restrict SSH access to specific IP addresses can prevent unauthorized access.
- Regular Updates: Keeping SSH software up to date ensures that security vulnerabilities are patched promptly.
By implementing these additional security measures, organizations can strengthen the protection of their IoT devices and minimize the risk of cyberattacks.
How to Set Up SSH for IoT Devices
Setting up SSH for IoT devices involves several steps, including installing the SSH server, configuring security settings, and testing the connection. Below is a step-by-step guide to help you get started:
- Install the SSH server on your IoT device, using a package manager or manual installation.
- Configure SSH settings, such as port number, encryption algorithms, and authentication methods.
- Set up key-based authentication to enhance security and eliminate the need for passwords.
- Test the SSH connection from a remote client to ensure secure and reliable access.
This setup process ensures that your IoT devices are securely configured for remote management and maintenance.
Benefits of Using SSH for IoT Devices
Using SSH for IoT devices offers numerous benefits, including:
- Enhanced Security: SSH provides strong encryption and authentication mechanisms, protecting IoT devices from unauthorized access.
- Remote Management: SSH enables secure remote access for device configuration, troubleshooting, and maintenance.
- Scalability: SSH can be easily scaled to accommodate growing IoT infrastructures, ensuring seamless operations.
These benefits make SSH an essential tool for securing and managing IoT devices, enhancing overall system performance and reliability.
Common Challenges and Solutions
While SSH is a powerful tool for securing IoT devices, there are several challenges that organizations may face. These include:
- Resource Constraints: IoT devices with limited resources may struggle to run resource-intensive SSH solutions. Using lightweight SSH clients like Dropbear can address this issue.
- Complexity: Configuring SSH settings and managing keys can be complex for inexperienced users. Providing training and documentation can help overcome this challenge.
- Cyber Threats: Despite SSH's robust security features, IoT devices remain vulnerable to advanced cyber threats. Regular updates and additional security measures can mitigate these risks.
By addressing these challenges proactively, organizations can ensure the successful implementation of SSH for their IoT devices.
The Future of Remote IoT Device SSH
As IoT continues to evolve, the role of SSH in securing remote IoT devices will become even more critical. Emerging technologies, such as quantum computing and blockchain, may influence the development of SSH protocols, offering new possibilities for enhanced security and efficiency.
Organizations should stay informed about the latest advancements in SSH technology and adapt their strategies accordingly. This will ensure that their IoT infrastructure remains secure and resilient in the face of evolving cyber threats.
Conclusion and Call to Action
In conclusion, best remote IoT device SSH solutions are essential for securing and managing IoT devices effectively. By understanding the basics of SSH, exploring the top solutions, and implementing additional security measures, organizations can protect their IoT infrastructure and ensure seamless operations.
We encourage readers to share their thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our website for more insights into IoT security and best practices. Together, we can build a safer and more connected world.