In today’s rapidly evolving digital landscape, securely connecting remote IoT devices through a Virtual Private Cloud (VPC) using Raspberry Pi and AWS has become a critical necessity for businesses and developers alike. As IoT devices continue to proliferate, ensuring secure communication between these devices and cloud infrastructure is paramount. In this guide, we will explore the step-by-step process of setting up a secure connection for remote IoT VPC using Raspberry Pi and AWS services.
Whether you’re a seasoned developer or just starting your journey into cloud computing and IoT, this guide will provide you with the knowledge and tools necessary to protect your IoT ecosystem. By leveraging AWS’s robust infrastructure and Raspberry Pi’s versatility, you can create a secure and scalable environment for your IoT projects.
This article delves into the technical aspects of securely connecting remote IoT devices, offering practical examples and actionable insights to help you achieve optimal results. Let’s dive in and explore the possibilities!
Read also:Kyle Larson Parents A Comprehensive Look Into Their Lives And Influence
Table of Contents
- Introduction to Secure IoT Connections
- Understanding AWS IoT Architecture
- Setting Up Raspberry Pi for IoT
- Overview of VPC in AWS
- How to Securely Connect IoT Devices
- Step-by-Step Guide to Implementation
- Best Practices for Secure IoT Connections
- Common Issues and Troubleshooting
- Real-World Case Studies
- Conclusion and Next Steps
Introduction to Secure IoT Connections
As the Internet of Things (IoT) continues to grow, ensuring secure connections between devices and cloud infrastructure is more important than ever. Securely connecting remote IoT VPC with Raspberry Pi on AWS provides a scalable solution for managing and protecting data transmission.
In this section, we will discuss:
- The importance of secure IoT connections.
- Why AWS and Raspberry Pi are ideal for IoT projects.
- Key benefits of using VPC for IoT security.
By the end of this section, you will have a foundational understanding of why securing IoT devices is critical for both personal and enterprise use cases.
Understanding AWS IoT Architecture
AWS offers a comprehensive suite of services designed specifically for IoT applications. Understanding the architecture of AWS IoT is essential for setting up a secure and efficient system.
Key Components of AWS IoT
The AWS IoT architecture includes several key components:
- AWS IoT Core: A managed cloud service that allows connected devices to securely interact with cloud applications and other devices.
- AWS IoT Device Management: Enables you to onboard, organize, monitor, and remotely manage IoT devices at scale.
- AWS IoT Analytics: Collects, processes, and analyzes IoT data, providing valuable insights for better decision-making.
These components work together to create a robust ecosystem for IoT applications.
Read also:Who Is Monica Lewinskys Husband Unveiling The Life And Relationship Of Monica Lewinsky
Setting Up Raspberry Pi for IoT
Raspberry Pi is a popular choice for IoT projects due to its affordability, flexibility, and ease of use. Setting up Raspberry Pi for IoT involves several steps:
Step 1: Hardware Requirements
Before starting, ensure you have the following hardware components:
- Raspberry Pi board (preferably Raspberry Pi 4).
- MicroSD card with Raspberry Pi OS installed.
- Power supply and necessary cables.
Step 2: Software Configuration
Once the hardware is ready, configure the software:
- Install necessary libraries and dependencies for IoT communication.
- Set up SSH for remote access.
- Configure Wi-Fi or Ethernet for network connectivity.
With these steps, your Raspberry Pi will be ready for IoT integration.
Overview of VPC in AWS
A Virtual Private Cloud (VPC) in AWS allows you to launch resources into a virtual network that you define. This provides enhanced security and control over your cloud resources.
Key Features of VPC
- Isolated network environment for your resources.
- Customizable IP address ranges and subnet configurations.
- Advanced security features, including security groups and network access control lists (ACLs).
By using VPC, you can ensure that your IoT devices communicate securely within a controlled environment.
How to Securely Connect IoT Devices
Securing IoT devices involves implementing multiple layers of protection. Here are some strategies to achieve a secure connection:
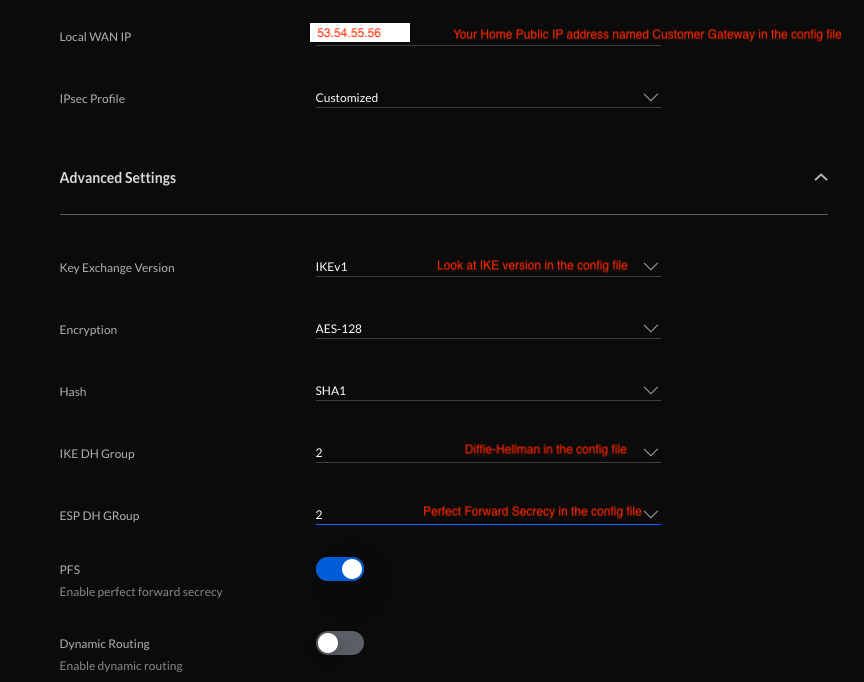
Data Encryption
Encrypting data in transit and at rest is crucial for protecting sensitive information. Use protocols such as TLS (Transport Layer Security) to secure communications between devices and the cloud.
Authentication and Authorization
Implement strong authentication mechanisms to verify the identity of devices and users. Use AWS IoT Core’s certificate-based authentication for secure device registration.
By combining these strategies, you can create a secure and reliable connection for your IoT devices.
Step-by-Step Guide to Implementation
Follow these steps to securely connect remote IoT VPC with Raspberry Pi on AWS:
Step 1: Set Up AWS Account
Create an AWS account and configure the necessary IAM roles and policies for IoT access.
Step 2: Create VPC
Design and deploy a VPC tailored to your IoT needs, ensuring proper subnet and security group configurations.
Step 3: Configure Raspberry Pi
Set up Raspberry Pi with the required software and libraries for IoT communication. Connect it to the AWS IoT Core service.
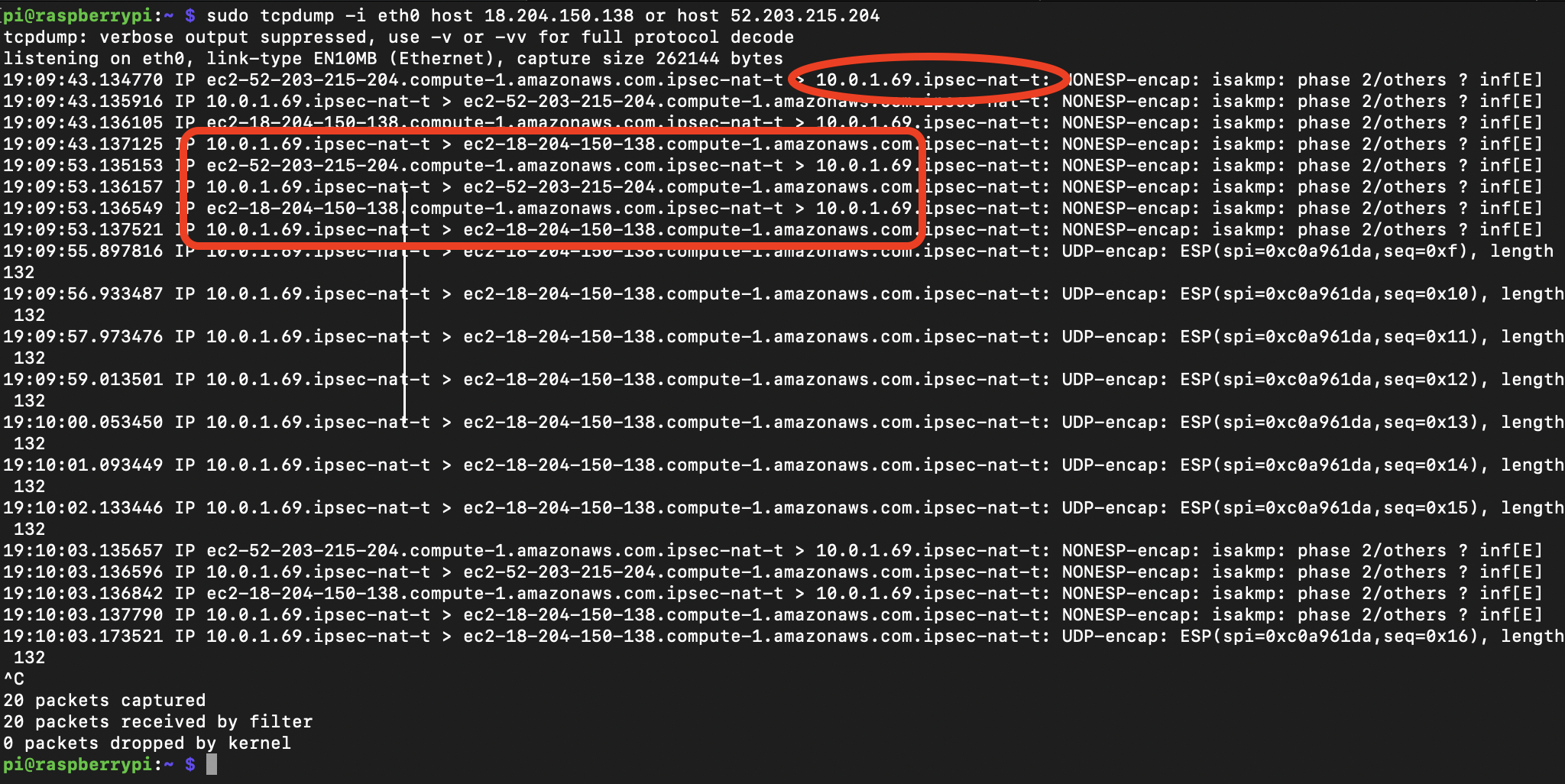
Step 4: Test and Monitor
Test the connection and monitor performance using AWS IoT Analytics and CloudWatch.
Following these steps will help you establish a secure and functional IoT environment.
Best Practices for Secure IoT Connections
To ensure the highest level of security for your IoT projects, consider the following best practices:
- Regularly update firmware and software on all devices.
- Implement robust access controls and restrict unnecessary permissions.
- Monitor network traffic for suspicious activity and respond promptly to potential threats.
By adhering to these practices, you can significantly reduce the risk of security breaches.
Common Issues and Troubleshooting
Even with careful planning, issues may arise during implementation. Here are some common problems and solutions:
Connection Issues
If devices fail to connect, check:
- Network configurations and firewall settings.
- Certificate validity and permissions.
Data Transmission Delays
To address delays, optimize:
- Data processing workflows.
- Network bandwidth and latency.
These troubleshooting tips will help you overcome challenges and maintain a stable connection.
Real-World Case Studies
Examining real-world examples can provide valuable insights into successful IoT implementations. Here are two case studies:
Case Study 1: Smart Agriculture
Agricultural company X implemented IoT sensors connected to Raspberry Pi and AWS VPC to monitor soil moisture levels. The secure connection ensured accurate data collection and analysis, leading to improved crop yields.
Case Study 2: Smart Home Automation
Homeowner Y used IoT devices with Raspberry Pi and AWS to automate lighting and temperature control. The secure setup provided peace of mind and energy savings.
These case studies demonstrate the versatility and effectiveness of securely connecting IoT devices using Raspberry Pi and AWS.
Conclusion and Next Steps
In conclusion, securely connecting remote IoT VPC with Raspberry Pi on AWS offers a powerful solution for managing and protecting IoT ecosystems. By following the steps and best practices outlined in this guide, you can create a secure and scalable environment for your IoT projects.
We encourage you to:
- Experiment with the techniques discussed in this article.
- Share your experiences and insights in the comments section.
- Explore other resources and tutorials for further learning.
Thank you for reading, and we hope this guide has been informative and helpful!
References:
- AWS IoT Documentation: https://docs.aws.amazon.com/iot/index.html
- Raspberry Pi Documentation: https://www.raspberrypi.org/documentation/
- IoT Security Best Practices: https://www.nist.gov/publications/iot-device-security-guidelines