Internet of Things (IoT) has revolutionized the way we interact with technology, and integrating SSH control on AWS is a game-changer for managing remote devices securely. If you're looking to enhance your IoT infrastructure with advanced security and scalability, this guide will walk you through everything you need to know about IoT SSH control on AWS. Whether you're a developer, system administrator, or tech enthusiast, this article is designed to provide you with actionable insights and practical knowledge.
In today's interconnected world, IoT devices are becoming increasingly common, and securing them is paramount. By leveraging AWS's robust infrastructure, you can implement SSH control to manage IoT devices remotely, ensuring both security and efficiency. This article delves into the intricacies of IoT SSH control on AWS, offering step-by-step guidance and expert tips to help you master this critical technology.
Whether you're new to IoT or an experienced professional, this comprehensive guide will provide you with the tools and knowledge to optimize your IoT SSH control on AWS. From setting up your environment to troubleshooting common issues, we've got you covered. Let's dive in and explore how IoT SSH control on AWS can transform your operations.
Read also:William Levy And Maite Perroni A Journey Through Their Love Story And Careers
Table of Contents
- Overview of IoT SSH Control on AWS
- AWS IoT Architecture for SSH Control
- Setting Up IoT SSH Control on AWS
- Enhancing Security in IoT SSH Control
- Tools and Technologies for IoT SSH Control
- Best Practices for Managing IoT SSH Control
- Troubleshooting Common Issues
- Scaling IoT SSH Control on AWS
- Real-World Use Cases
- The Future of IoT SSH Control on AWS
Overview of IoT SSH Control on AWS
IoT SSH control on AWS refers to the process of managing and securing IoT devices using SSH (Secure Shell) protocols within the Amazon Web Services ecosystem. This approach allows administrators to remotely access and configure IoT devices with enhanced security measures. By leveraging AWS's scalable infrastructure, organizations can efficiently manage large fleets of IoT devices while maintaining robust security protocols.
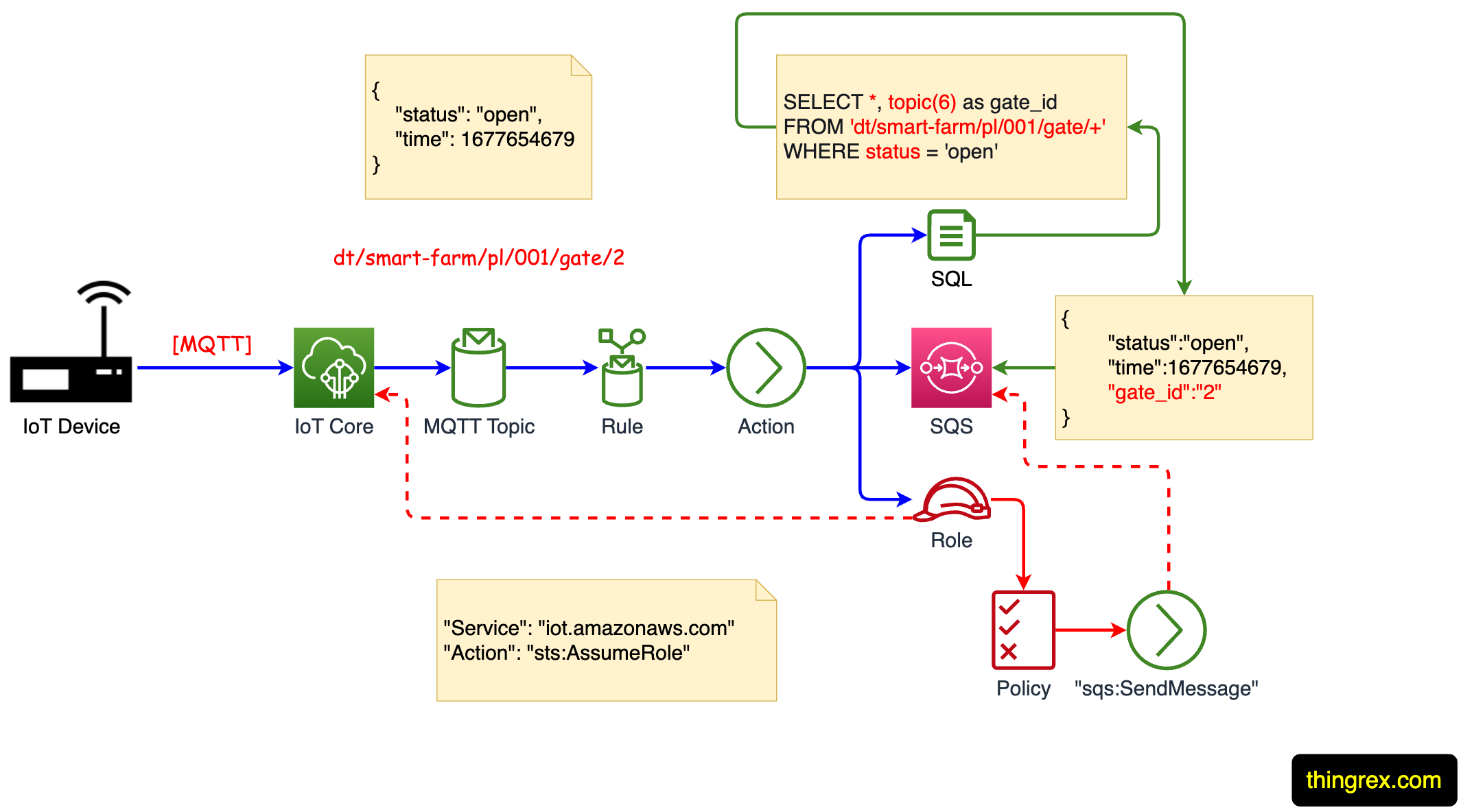
SSH control is particularly valuable in IoT environments where devices are distributed across various locations. It provides a secure channel for communication, ensuring that sensitive data remains protected from unauthorized access. AWS offers a range of services that integrate seamlessly with IoT SSH control, such as AWS IoT Core, AWS Lambda, and Amazon EC2, enabling businesses to build scalable and secure IoT solutions.
Why Choose AWS for IoT SSH Control?
- Scalability: AWS's infrastructure can handle millions of IoT devices simultaneously.
- Security: Advanced security features, such as encryption and identity management, ensure data protection.
- Integration: Seamless integration with other AWS services enhances functionality and efficiency.
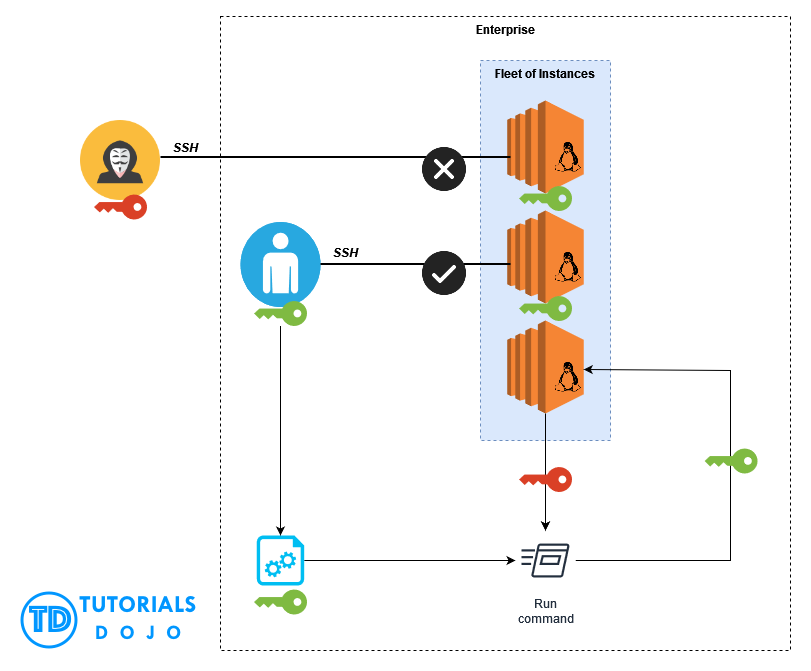
AWS IoT Architecture for SSH Control
The architecture for IoT SSH control on AWS involves several key components that work together to ensure secure and efficient device management. These components include AWS IoT Core, Amazon EC2 instances, and AWS Lambda functions, among others. Understanding this architecture is crucial for implementing a successful IoT SSH control solution.
Key Components
- AWS IoT Core: Acts as the central hub for device communication and management.
- Amazon EC2: Provides the computational resources needed for SSH sessions.
- AWS Lambda: Enables serverless computing for automating tasks and managing device interactions.
Setting Up IoT SSH Control on AWS
Setting up IoT SSH control on AWS involves several steps, from configuring AWS IoT Core to establishing secure SSH connections. Below is a step-by-step guide to help you get started:
Step 1: Create an AWS IoT Core Account
Begin by creating an AWS account and enabling AWS IoT Core. This service will serve as the foundation for managing your IoT devices.
Step 2: Configure Security Credentials
Set up security credentials, including certificates and policies, to ensure secure communication between devices and the AWS cloud.
Read also:Deion Sanders Wife A Comprehensive Look At The Life And Legacy
Step 3: Deploy EC2 Instances
Launch EC2 instances to host SSH servers that will manage remote access to IoT devices. Configure these instances with appropriate security groups and firewall rules.
Enhancing Security in IoT SSH Control
Security is a top priority when managing IoT devices with SSH control on AWS. Implementing best practices for security can significantly reduce the risk of unauthorized access and data breaches.
Best Security Practices
- Use strong, unique passwords and implement two-factor authentication (2FA).
- Regularly update and patch your systems to protect against vulnerabilities.
- Monitor network activity for suspicious behavior using AWS CloudWatch.
Tools and Technologies for IoT SSH Control
A variety of tools and technologies are available to facilitate IoT SSH control on AWS. These tools enhance productivity and streamline the management of IoT devices.
Popular Tools
- AWS IoT Device Management: Simplifies device provisioning and monitoring.
- SSH Key Management: Ensures secure key exchange and storage.
- Amazon CloudWatch: Provides real-time monitoring and logging capabilities.
Best Practices for Managing IoT SSH Control
To effectively manage IoT SSH control on AWS, it's essential to follow best practices that promote efficiency and security. These practices include regular maintenance, thorough documentation, and continuous monitoring.
Key Best Practices
- Document all configurations and procedures for easy reference.
- Perform regular audits to identify and address potential security risks.
- Train staff on proper SSH control practices to minimize human error.
Troubleshooting Common Issues
Even with the best planning and implementation, issues can arise when managing IoT SSH control on AWS. Below are some common problems and their solutions:
Connection Issues
- Check network configurations and ensure proper firewall settings.
- Verify that SSH keys are correctly configured and up-to-date.
Performance Problems
- Optimize EC2 instance types to match workload requirements.
- Use AWS Auto Scaling to handle fluctuations in demand.
Scaling IoT SSH Control on AWS
As your IoT fleet grows, it's important to scale your SSH control solution to accommodate additional devices and traffic. AWS provides several scaling options to ensure smooth operations.
Scaling Strategies
- Use AWS Auto Scaling to dynamically adjust resources based on demand.
- Implement load balancing to distribute traffic evenly across servers.
Real-World Use Cases
IoT SSH control on AWS has been successfully implemented in various industries, offering innovative solutions to complex challenges. Below are some real-world use cases:
Smart Cities
Smart cities utilize IoT SSH control on AWS to manage infrastructure such as lighting, traffic systems, and public transportation, improving efficiency and reducing costs.
Industrial Automation
In manufacturing, IoT SSH control on AWS enables remote monitoring and maintenance of machinery, enhancing productivity and reducing downtime.
The Future of IoT SSH Control on AWS
The future of IoT SSH control on AWS looks promising, with advancements in technology driving innovation and efficiency. As more organizations adopt IoT solutions, the demand for secure and scalable SSH control will continue to grow.
Emerging trends, such as edge computing and artificial intelligence, will further enhance the capabilities of IoT SSH control on AWS, paving the way for smarter, more connected ecosystems.
Conclusion
In conclusion, mastering IoT SSH control on AWS is essential for anyone looking to optimize their IoT infrastructure. By following the guidelines and best practices outlined in this article, you can ensure secure and efficient management of your IoT devices. Remember to regularly update your systems, monitor for potential threats, and stay informed about the latest advancements in IoT technology.
We invite you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other articles on our site for more insights into IoT and AWS technologies. Together, let's build a smarter, more connected future!
Data Sources: