In today's interconnected world, managing IoT devices securely is a critical task for organizations. The ability to access SSH IoT device anywhere through AWS provides unparalleled flexibility and security. As remote access becomes increasingly essential, understanding how to implement this functionality effectively is vital for maintaining operational efficiency and safeguarding sensitive data.
With the rapid growth of the Internet of Things (IoT), businesses are leveraging AWS services to streamline their operations and ensure seamless device management. This article delves into the concept of accessing SSH IoT devices from anywhere using AWS, highlighting the benefits, challenges, and best practices associated with this approach. By the end of this guide, you will have a clear understanding of how to set up and manage SSH access for IoT devices securely.
This comprehensive guide is designed to equip you with the knowledge and tools necessary to implement secure and efficient SSH access for IoT devices using AWS. Whether you're a developer, system administrator, or IT professional, this article will provide valuable insights and practical advice to enhance your IoT infrastructure.
Read also:Brigitte Macron As A Child The Early Life Of Frances First Lady
Table of Contents
- Introduction to SSH IoT Device Access
- Why AWS is Ideal for SSH IoT Device Access
- Setting Up SSH IoT Device Access on AWS
- Security Best Practices for SSH IoT Devices
- Example Implementation of SSH IoT Device Access
- Troubleshooting Tips for SSH IoT Devices
- Cost Considerations for AWS SSH IoT Devices
- Scaling Your SSH IoT Device Solution
- Future Trends in SSH IoT Device Management
- Conclusion and Next Steps
Introduction to SSH IoT Device Access
SSH (Secure Shell) is a cryptographic network protocol used to establish secure connections between devices over an unsecured network. When it comes to IoT devices, SSH provides a reliable method for remote access and management. The ability to access SSH IoT device anywhere is particularly useful for monitoring, troubleshooting, and maintaining devices deployed in remote locations.
Benefits of SSH for IoT Devices
Using SSH for IoT devices offers several advantages:
- Enhanced security through encryption
- Remote access capabilities
- Efficient device management
- Compatibility with various operating systems
Challenges of Implementing SSH IoT Device Access
While SSH offers numerous benefits, there are challenges to consider:
- Security risks if not properly configured
- Complexity in managing large-scale deployments
- Network latency issues
Why AWS is Ideal for SSH IoT Device Access
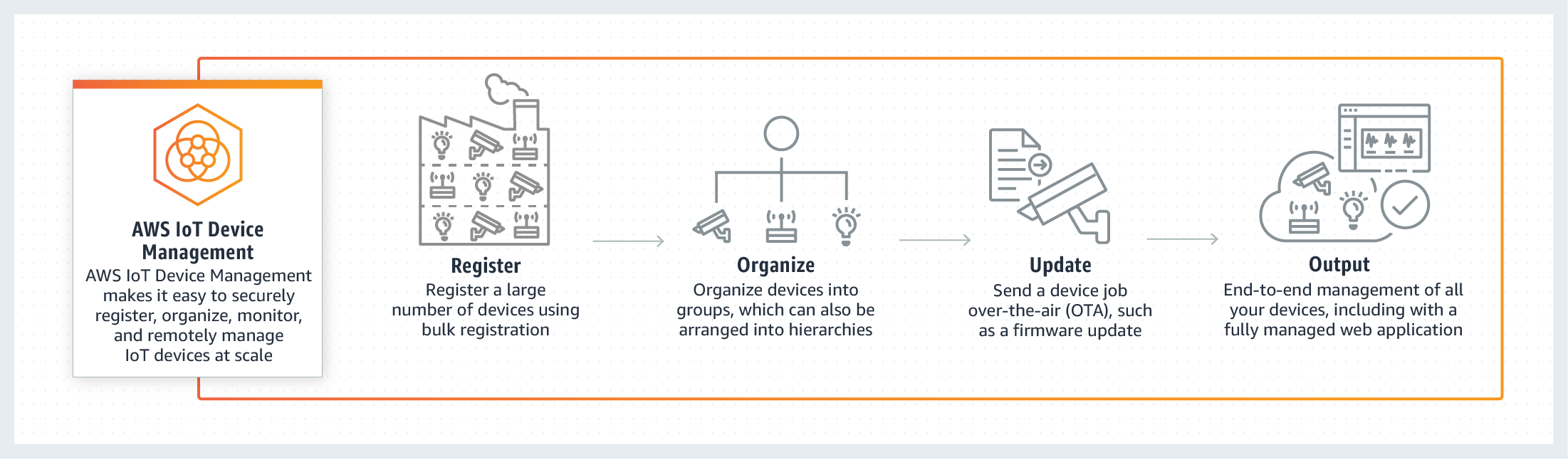
AWS provides a robust platform for managing SSH IoT device access. With its extensive suite of services, AWS enables secure and scalable remote access to IoT devices. Key features that make AWS ideal for SSH IoT device access include:
1. AWS IoT Core
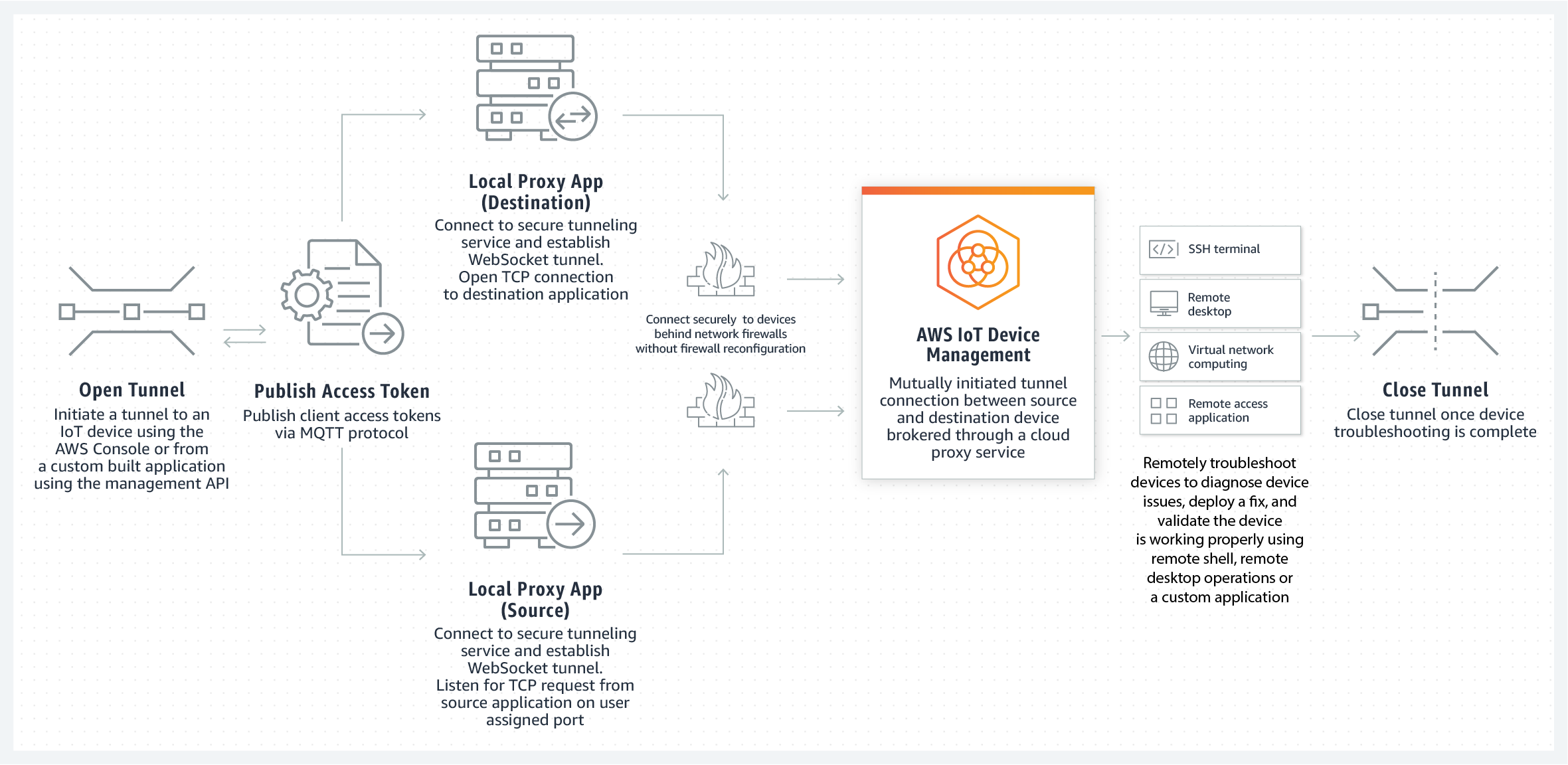
AWS IoT Core facilitates secure communication between devices and the cloud. It supports MQTT, HTTP, and WebSocket protocols, making it versatile for various IoT use cases.
2. AWS Systems Manager
AWS Systems Manager allows you to remotely manage and troubleshoot IoT devices. This service simplifies the process of accessing SSH IoT device anywhere by providing a centralized interface for device management.
Read also:Carys Zeta Douglas The Rising Star In The Entertainment Industry
3. AWS Identity and Access Management (IAM)
AWS IAM ensures secure access to AWS resources by defining and managing user permissions. By integrating IAM with SSH IoT device access, you can implement role-based access control and enhance security.
Setting Up SSH IoT Device Access on AWS
Setting up SSH IoT device access on AWS involves several steps. Below is a detailed guide to help you configure this functionality effectively.
Step 1: Provisioning IoT Devices
Before enabling SSH access, you need to provision your IoT devices. This involves:
- Registering devices with AWS IoT Core
- Assigning unique identities and certificates
Step 2: Configuring SSH on IoT Devices
Ensure that SSH is installed and configured on your IoT devices. Use the following commands to set up SSH:
Install SSH server: sudo apt-get install openssh-server
Start SSH service: sudo service ssh start
Step 3: Establishing Secure Connections
To establish secure connections, use AWS Systems Manager to create a session for accessing SSH IoT device anywhere. This method eliminates the need for public IP addresses and ensures secure communication.
Security Best Practices for SSH IoT Devices
Implementing robust security measures is crucial when accessing SSH IoT device anywhere. Follow these best practices to protect your devices and data:
1. Use Strong Passwords and Key-Based Authentication
Enforce the use of strong passwords and consider implementing key-based authentication for added security.
2. Regularly Update Firmware and Software
Keep your IoT devices up to date with the latest firmware and software updates to address vulnerabilities.
3. Monitor and Audit Access Logs
Regularly review access logs to detect and respond to unauthorized access attempts promptly.
Example Implementation of SSH IoT Device Access
Let's explore a practical example of setting up SSH IoT device access using AWS. In this scenario, we will configure an IoT device running on a Raspberry Pi to allow remote access via SSH.
Step 1: Register the Device with AWS IoT Core
Follow the AWS IoT Core documentation to register your Raspberry Pi and generate necessary certificates.
Step 2: Configure SSH on Raspberry Pi
Install and configure the SSH server on your Raspberry Pi using the commands mentioned earlier.
Step 3: Access the Device Using AWS Systems Manager
Use AWS Systems Manager to create a session and access the Raspberry Pi remotely. This method ensures secure and seamless access without exposing the device to the public internet.
Troubleshooting Tips for SSH IoT Devices
Encountering issues while accessing SSH IoT device anywhere is common. Here are some troubleshooting tips to help you resolve common problems:
1. Connection Issues
Verify network connectivity and ensure that the necessary ports are open. Check firewall settings and security groups to allow SSH traffic.
2. Authentication Failures
Double-check usernames, passwords, and SSH keys. Ensure that the correct credentials are being used for authentication.
3. Performance Problems
Optimize your network configuration and consider using AWS CloudFront to reduce latency and improve performance.
Cost Considerations for AWS SSH IoT Devices
Understanding the cost implications of implementing SSH IoT device access on AWS is essential for budget planning. AWS offers a pay-as-you-go pricing model, making it cost-effective for businesses of all sizes.
1. AWS IoT Core Pricing
AWS IoT Core charges based on the number of messages processed and the number of devices connected.
2. AWS Systems Manager Pricing
AWS Systems Manager charges for the number of managed instances and the amount of data transferred.
Scaling Your SSH IoT Device Solution
As your IoT infrastructure grows, scaling your SSH IoT device solution becomes necessary. AWS provides several tools and services to help you scale efficiently:
1. AWS Auto Scaling
Automatically adjust resources to meet demand and ensure optimal performance.
2. AWS Lambda
Use AWS Lambda to automate tasks and reduce the need for manual intervention.
Future Trends in SSH IoT Device Management
The field of SSH IoT device management is evolving rapidly. Emerging trends include:
1. Edge Computing
Edge computing enables processing data closer to the source, reducing latency and improving performance.
2. Artificial Intelligence and Machine Learning
AI and ML technologies are being integrated into IoT systems to enhance predictive maintenance and anomaly detection.
Conclusion and Next Steps
Accessing SSH IoT device anywhere using AWS offers significant benefits for businesses looking to manage their IoT infrastructure effectively. By following the guidelines and best practices outlined in this article, you can implement a secure and scalable solution tailored to your needs.
We encourage you to take the following actions:
- Experiment with the example implementation to gain hands-on experience.
- Explore additional AWS services to enhance your IoT solution.
- Share your thoughts and feedback in the comments section below.
Thank you for reading this comprehensive guide. We hope it has provided valuable insights into SSH IoT device access using AWS. Stay tuned for more articles on IoT and cloud computing topics.