As the Internet of Things (IoT) continues to grow, securely connecting remote IoT devices using peer-to-peer (P2P) SSH on Android has become a critical need for developers and users alike. The ability to establish secure connections ensures data integrity and minimizes the risk of unauthorized access. In this article, we will explore the essential aspects of securely connecting IoT devices through P2P SSH on Android, providing actionable insights and best practices.
This guide delves into the technicalities of IoT security, focusing on the importance of P2P SSH connections for Android devices. By understanding the underlying mechanisms, users can protect their devices from potential cyber threats while maintaining seamless connectivity. Whether you're a developer or an end-user, this article offers valuable information to enhance your IoT security strategy.
With the increasing reliance on connected devices, ensuring secure communication channels is paramount. This article will cover everything from basic concepts to advanced techniques, ensuring that you are equipped with the knowledge to implement robust security measures for your IoT ecosystem.
Read also:How Old Is Tim Mcgraw A Comprehensive Guide To His Age Career And Life
Table of Contents
- Introduction to Secure IoT Connections
- Overview of IoT and Its Challenges
- Understanding P2P SSH and Its Role
- Implementing P2P SSH on Android
- Best Practices for Secure Connections
- Common Vulnerabilities in IoT Security
- Tools and Techniques for Enhanced Security
- Protecting Data in IoT Ecosystems
- Future Trends in IoT Security
- Conclusion and Call to Action
Introduction to Secure IoT Connections
The rise of IoT has transformed the way devices communicate and interact with each other. However, this rapid growth also brings significant security challenges. Securely connect remote IoT P2P SSH Android solutions are vital for maintaining privacy and protecting sensitive data. By leveraging SSH protocols, users can establish encrypted connections that safeguard against unauthorized access.
In this section, we will explore the fundamental principles of secure IoT connections and why they are crucial in today's digital landscape. Understanding the basics of SSH and its application in IoT systems is the first step toward building a secure infrastructure.
Why Security Matters in IoT
IoT devices are often deployed in environments where they handle sensitive information, such as personal data, financial transactions, and health records. Without proper security measures, these devices can become entry points for cyberattacks. Secure connections using SSH protocols help mitigate these risks by encrypting data during transmission and authenticating devices.
Overview of IoT and Its Challenges
The Internet of Things encompasses a wide range of devices, from smart home appliances to industrial sensors. While IoT offers numerous benefits, it also introduces unique challenges, particularly in terms of security. Ensuring that IoT devices can securely connect remote P2P SSH Android is a complex task that requires a multi-layered approach.
Challenges in IoT Security
- Limited computational resources on IoT devices
- Fragmented standards and protocols
- Scalability issues in large-scale IoT deployments
- Increased attack surface due to interconnected devices
Understanding P2P SSH and Its Role
P2P SSH (Secure Shell) is a protocol designed to facilitate secure communication between devices over a network. By implementing P2P SSH, users can securely connect remote IoT devices on Android platforms, ensuring data integrity and confidentiality. This section will delve into the technical aspects of P2P SSH and its significance in IoT security.
How P2P SSH Works
P2P SSH establishes a direct connection between two devices without relying on a central server. This approach reduces latency and enhances security by minimizing potential points of failure. Key features of P2P SSH include:
Read also:Aoc Net Worth Exploring The Wealth And Influence Of Alexandria Ocasiocortez
- End-to-end encryption
- Authentication mechanisms
- Secure key exchange
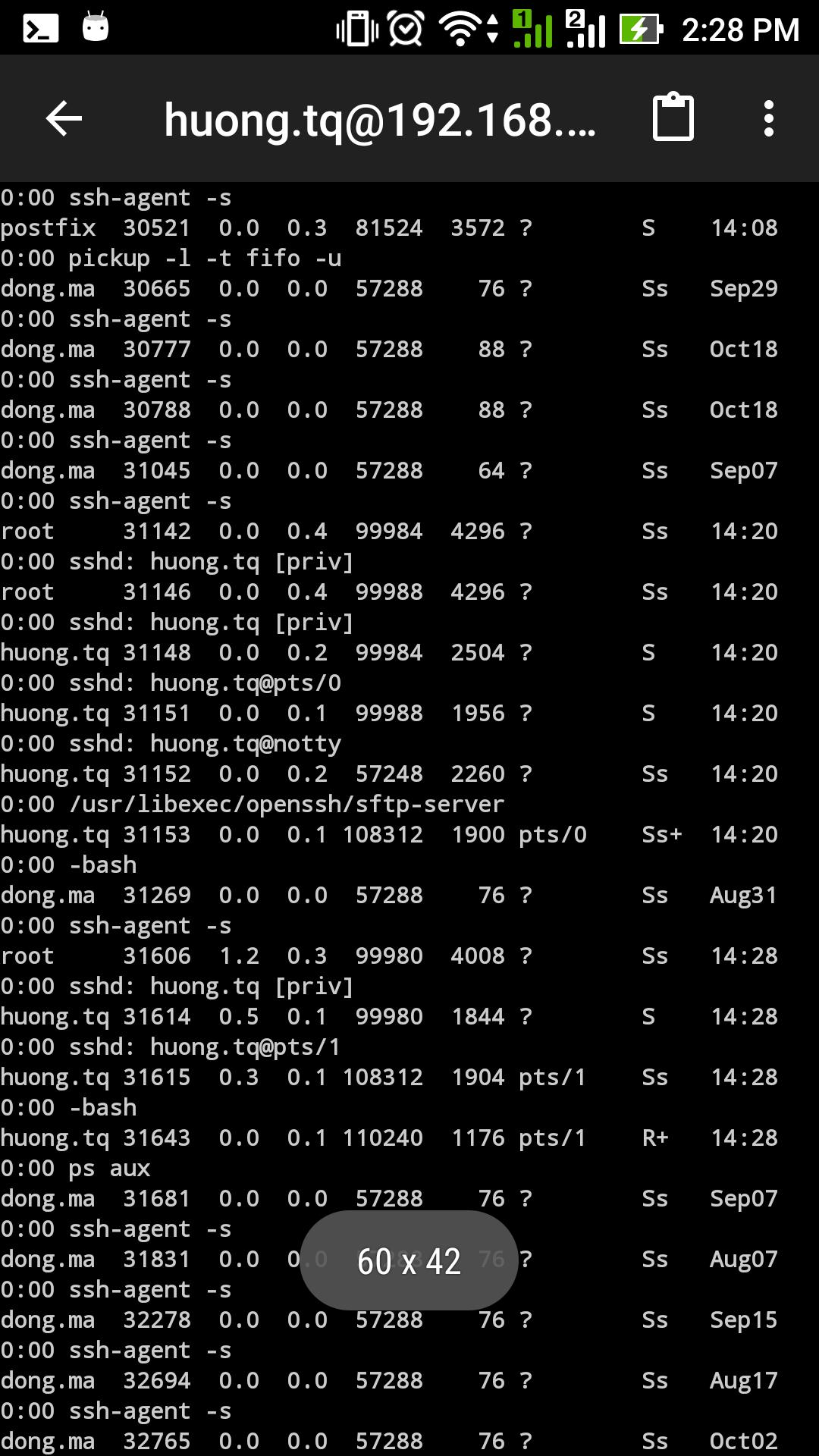
Implementing P2P SSH on Android
Android devices are increasingly being used as gateways for IoT ecosystems. To securely connect remote IoT devices, developers can leverage P2P SSH protocols. This section will outline the steps required to implement P2P SSH on Android platforms, including necessary libraries and tools.
Steps to Implement P2P SSH
- Install an SSH client library on your Android device
- Generate SSH keys for authentication
- Configure the SSH server on the IoT device
- Establish a secure connection between the devices
Best Practices for Secure Connections
Implementing P2P SSH is just the first step toward securing your IoT ecosystem. To ensure long-term protection, it is essential to follow best practices in IoT security. This section will provide actionable advice for enhancing the security of your IoT connections.
Key Best Practices
- Regularly update firmware and software
- Use strong, unique passwords for authentication
- Implement two-factor authentication (2FA) wherever possible
- Monitor network activity for suspicious behavior
Common Vulnerabilities in IoT Security
Despite advancements in security technologies, IoT devices remain vulnerable to various threats. This section will highlight common vulnerabilities in IoT systems and provide strategies for mitigating these risks.
Identifying Vulnerabilities
Some of the most prevalent vulnerabilities in IoT security include:
- Weak default credentials
- Unpatched software vulnerabilities
- Insecure data storage practices
- Lack of network segmentation
Tools and Techniques for Enhanced Security
To further strengthen your IoT security posture, it is important to utilize specialized tools and techniques. This section will introduce you to some of the most effective tools for securing IoT connections, including firewalls, intrusion detection systems, and encryption protocols.
Recommended Tools
- Wireshark for network analysis
- OpenSSH for secure communication
- Snort for intrusion detection
Protecting Data in IoT Ecosystems
Data protection is a critical component of IoT security. By securely connecting remote IoT P2P SSH Android devices, users can ensure that sensitive information remains protected. This section will explore strategies for safeguarding data in IoT ecosystems, including encryption, access control, and data anonymization.
Data Protection Strategies
- Encrypt data both in transit and at rest
- Implement role-based access control
- Regularly audit data access logs
Future Trends in IoT Security
As technology continues to evolve, so too will the methods used to secure IoT devices. This section will examine emerging trends in IoT security, such as blockchain, artificial intelligence, and quantum cryptography, and their potential impact on the future of secure IoT connections.
Emerging Technologies
- Blockchain for decentralized security
- AI-driven threat detection
- Quantum-resistant encryption algorithms
Conclusion and Call to Action
In conclusion, securely connecting remote IoT P2P SSH Android devices is essential for maintaining the integrity and security of your IoT ecosystem. By following the best practices outlined in this article and leveraging advanced tools and techniques, you can protect your devices from potential threats.
We encourage you to take action by implementing the strategies discussed in this guide. Leave a comment below to share your thoughts or ask questions. Additionally, consider exploring other articles on our website for more insights into IoT security and related topics.
References:
- IEEE: "Security Challenges in IoT" (https://www.ieee.org)
- NIST: "IoT Security Guidelines" (https://www.nist.gov)
- OpenSSH Documentation (https://www.openssh.com)