Connecting remote IoT devices through secure protocols like SSH on Android has become increasingly important as the world becomes more interconnected. Whether you're a tech enthusiast, a developer, or simply someone looking to enhance your cybersecurity knowledge, this guide will provide comprehensive insights into securely connecting IoT devices using P2P SSH on Android. Learn how to download and implement these tools effectively.
In today's digital age, Internet of Things (IoT) devices are becoming an integral part of our daily lives. From smart homes to industrial applications, IoT devices offer convenience and efficiency. However, ensuring the security of these devices is paramount, especially when connecting them remotely. This article delves into the best practices for securely connecting remote IoT devices using peer-to-peer (P2P) SSH on Android.
Whether you're looking to set up a secure connection for your smart home devices or managing industrial IoT networks, understanding the mechanisms behind remote IoT P2P SSH connections is crucial. This guide will walk you through everything you need to know, including downloading and implementing secure SSH tools on Android devices.
Read also:Is Goregrish Illegal Unpacking The Legal Cultural And Ethical Dimensions
Table of Contents
- Introduction to Remote IoT Connections
- Understanding P2P SSH
- Why Android for Remote IoT Connections
- Securely Connect Remote IoT Devices
- Tools for SSH on Android
- Step-by-Step Guide to Setting Up SSH
- Downloading SSH Tools
- Best Practices for Secure Connections
- Troubleshooting Tips
- Conclusion
Introduction to Remote IoT Connections
IoT devices are transforming how we interact with technology. These devices are designed to communicate and share data over the internet, making it possible to control them remotely. However, remote connectivity introduces security risks, which is why secure connections are essential.
What Are Remote IoT Connections?
Remote IoT connections allow users to access and manage IoT devices from anywhere in the world. This is particularly useful for monitoring and controlling devices such as smart thermostats, security cameras, and industrial sensors. Ensuring these connections are secure is critical to prevent unauthorized access and data breaches.
Why Security Matters in IoT?
IoT devices often handle sensitive data, making them prime targets for cybercriminals. A secure connection ensures that data transmitted between devices remains private and protected from malicious actors. By using protocols like SSH, users can establish encrypted connections that safeguard their data.
Understanding P2P SSH
Peer-to-peer (P2P) SSH is a secure method for connecting IoT devices directly without relying on centralized servers. SSH, or Secure Shell, is a cryptographic network protocol that provides a secure channel over an unsecured network.
How Does P2P SSH Work?
- P2P SSH establishes a direct connection between two devices.
- Data is encrypted during transmission, ensuring privacy and security.
- The protocol authenticates devices before allowing access, reducing the risk of unauthorized connections.
Advantages of Using P2P SSH
- Enhanced security through encryption.
- Reduced reliance on third-party servers.
- Improved performance due to direct connections.
Why Android for Remote IoT Connections
Android devices offer a versatile platform for managing remote IoT connections. With a wide range of apps and tools available, users can easily set up secure connections on their smartphones or tablets.
Features That Make Android Ideal for IoT
- Open-source architecture that supports customization.
- Availability of SSH apps in the Google Play Store.
- Compatibility with various IoT protocols and standards.
Securely Connect Remote IoT Devices
Establishing a secure connection for remote IoT devices involves several steps. By following best practices, users can ensure their devices remain protected from potential threats.
Read also:Is Henry Cavill The New James Bond
Steps to Secure IoT Connections
- Use strong passwords and authentication methods.
- Regularly update firmware and software to patch vulnerabilities.
- Implement firewalls and intrusion detection systems.
Choosing the Right Protocol
Selecting the appropriate protocol for your IoT devices is crucial. SSH is one of the most secure options available, offering robust encryption and authentication features.
Tools for SSH on Android
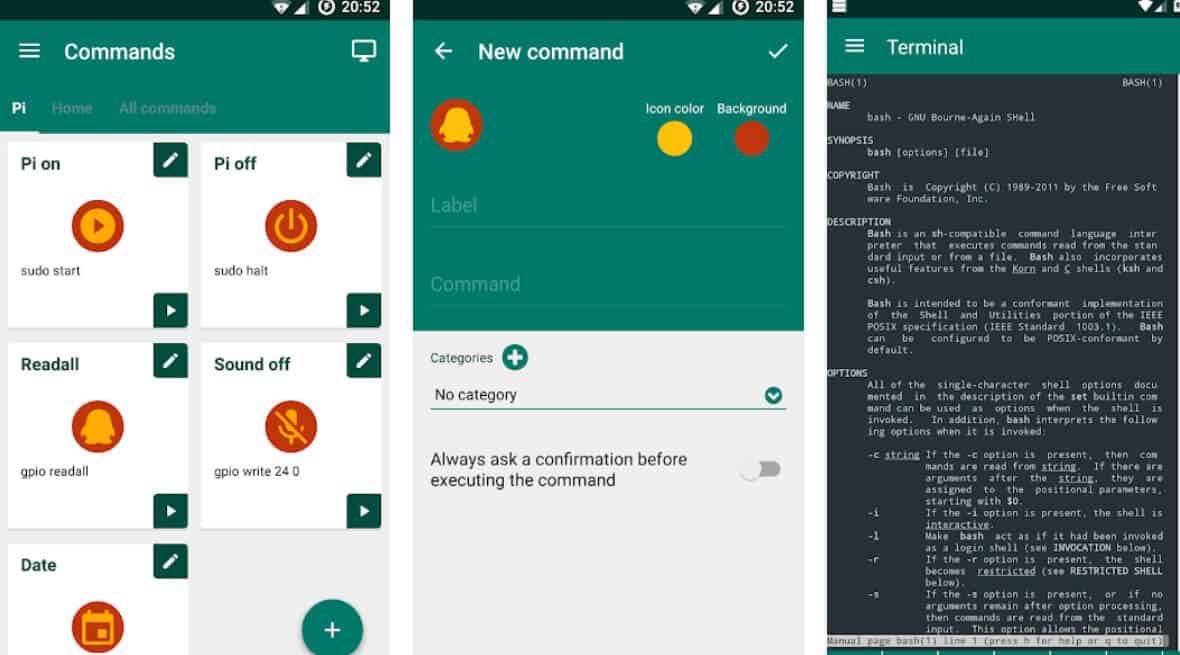
Several apps and tools are available for setting up SSH connections on Android devices. These tools simplify the process of securely connecting remote IoT devices.
Popular SSH Apps for Android
- Termux: A powerful terminal emulator and Linux environment app.
- SSHClient: A user-friendly app for managing SSH connections.
- JuiceSSH: A feature-rich app with a clean interface.
Key Features to Look For
- Support for multiple protocols, including SSH and SFTP.
- Customizable connection settings.
- Strong encryption and authentication options.
Step-by-Step Guide to Setting Up SSH
Setting up SSH on an Android device involves a few straightforward steps. By following this guide, users can establish secure connections for their IoT devices.
Step 1: Install an SSH App
Download and install a reliable SSH app from the Google Play Store. Popular choices include Termux, SSHClient, and JuiceSSH.
Step 2: Configure SSH Settings
Once the app is installed, configure the SSH settings to match your device's requirements. This includes specifying the server address, port number, and authentication method.
Step 3: Test the Connection
After configuring the settings, test the connection to ensure it is working correctly. Most SSH apps provide a connection testing feature to verify connectivity.
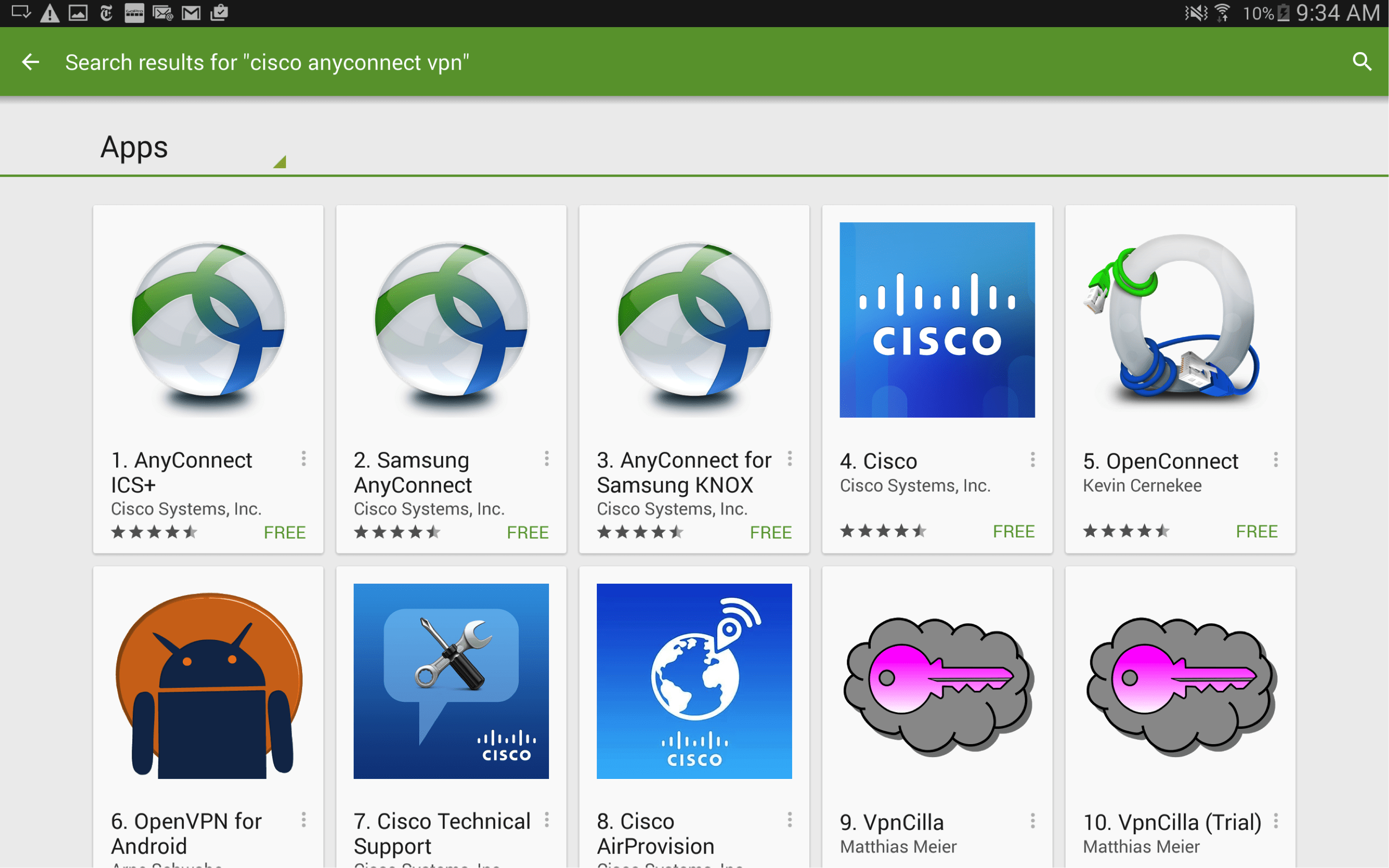
Downloading SSH Tools
Downloading SSH tools on Android is simple and can be done directly from the Google Play Store. Users should ensure they download apps from reputable developers to avoid security risks.
Recommended Download Sources
- Google Play Store: The official app store for Android devices.
- Developer Websites: Some developers offer direct downloads from their official websites.
Verifying App Authenticity
Before downloading any app, verify its authenticity by checking user reviews and developer credentials. This helps ensure the app is safe and reliable.
Best Practices for Secure Connections
Implementing best practices for secure connections is essential for protecting IoT devices. By following these guidelines, users can minimize the risk of security breaches.
Regularly Update Software
Keep all software and firmware up to date to patch known vulnerabilities and improve security.
Use Strong Authentication Methods
Implement multi-factor authentication (MFA) and use strong, unique passwords for added security.
Monitor Network Activity
Regularly monitor network activity for any suspicious behavior and take immediate action if potential threats are detected.
Troubleshooting Tips
Encountering issues while setting up SSH connections is common. Here are some troubleshooting tips to help resolve common problems.
Connection Issues
- Verify the server address and port number.
- Check firewall settings to ensure they are not blocking the connection.
- Restart the SSH app and try connecting again.
Authentication Failures
- Ensure the correct username and password are entered.
- Check if the authentication method is supported by the server.
- Reset the authentication settings and try again.
Conclusion
Securing remote IoT connections using P2P SSH on Android is vital for protecting sensitive data and preventing unauthorized access. By following the steps outlined in this guide, users can establish secure connections and enhance their cybersecurity.
We encourage readers to share their experiences and ask questions in the comments section below. Additionally, consider exploring other articles on our site for more insights into IoT security and related topics. Together, we can create a safer digital world.