In today's interconnected world, securely connecting remote IoT devices using P2P SSH on Android for free has become a necessity. Whether you're a hobbyist, developer, or enterprise professional, ensuring secure communication is paramount. This guide will walk you through the essential steps and tools required to set up secure connections while keeping costs minimal.
As the Internet of Things (IoT) continues to expand, the need for secure remote access to devices grows exponentially. With billions of connected devices worldwide, ensuring data integrity and privacy is no longer optional but a fundamental requirement. This article will explore how you can securely connect remote IoT devices using P2P SSH on Android without incurring additional costs.
Whether you're managing smart home devices, industrial sensors, or personal gadgets, this guide will provide actionable insights and practical solutions. By the end of this article, you'll have a clear understanding of how to establish secure connections, protect your data, and leverage free tools to streamline your IoT operations.
Read also:Jake Ream Age Exploring The Life And Career Of A Rising Star
Table of Contents
- Introduction to Secure IoT Connections
- Understanding IoT and Its Challenges
- What is P2P SSH and Why Use It?
- Android as a Platform for IoT Connections
- Free Tools for Secure Connections
- Step-by-Step Setup Guide
- Enhancing Security Measures
- Common Issues and Troubleshooting
- The Future of IoT Security
- Conclusion and Call to Action
Introduction to Secure IoT Connections
IoT devices are transforming the way we interact with technology. However, with this transformation comes the challenge of ensuring secure communication between devices. Securely connect remote IoT P2P SSH Android free solutions offer a practical approach to managing this challenge. Let's delve deeper into the importance of secure connections and how they can be achieved.
Why Security Matters in IoT
IoT devices often handle sensitive data, from personal health information to industrial automation data. A breach in security can lead to significant financial losses and reputational damage. By using P2P SSH, you can encrypt data transmissions, ensuring that only authorized parties can access the information.
The Role of SSH in IoT
SSH (Secure Shell) is a protocol designed for secure data communication. It provides a robust framework for securing remote connections, making it ideal for IoT applications. With SSH, you can establish encrypted tunnels that protect your data from unauthorized access.
Understanding IoT and Its Challenges
The Internet of Things (IoT) refers to the network of physical devices embedded with sensors, software, and connectivity, enabling them to exchange data. While IoT brings immense benefits, it also introduces unique challenges, particularly in the realm of security.
Key Challenges in IoT Security
- Data Privacy: Protecting sensitive information transmitted between devices.
- Device Authentication: Ensuring only authorized devices can communicate.
- Network Vulnerabilities: Preventing unauthorized access to the network.
What is P2P SSH and Why Use It?
P2P (Peer-to-Peer) SSH allows devices to communicate directly without relying on a central server. This approach reduces latency and enhances security by minimizing potential attack vectors.
Benefits of P2P SSH
- Decentralized Communication: Devices communicate directly, reducing reliance on intermediaries.
- Enhanced Security: Encrypted connections ensure data privacy.
- Cost-Effective: Eliminates the need for expensive server infrastructure.
Android as a Platform for IoT Connections
Android has emerged as a leading platform for IoT applications due to its flexibility and wide adoption. With Android, you can develop apps that seamlessly integrate with IoT devices, enabling secure remote access.
Read also:Blue Ivy And Cathy White A Journey Through Music Influence And Legacy
Advantages of Using Android for IoT
- Open Source: Android's open-source nature allows for customization and innovation.
- Large Developer Community: Access to a vast network of developers and resources.
- Compatibility: Android devices are compatible with a wide range of IoT platforms.
Free Tools for Secure Connections
Several free tools are available to help you establish secure connections between IoT devices. These tools leverage P2P SSH and other encryption protocols to ensure data integrity.
Recommended Tools
- Termux: A powerful terminal emulator for Android that supports SSH.
- OpenSSH: A widely used SSH client and server software.
- WireGuard: A modern VPN solution that enhances security for IoT connections.
Step-by-Step Setup Guide
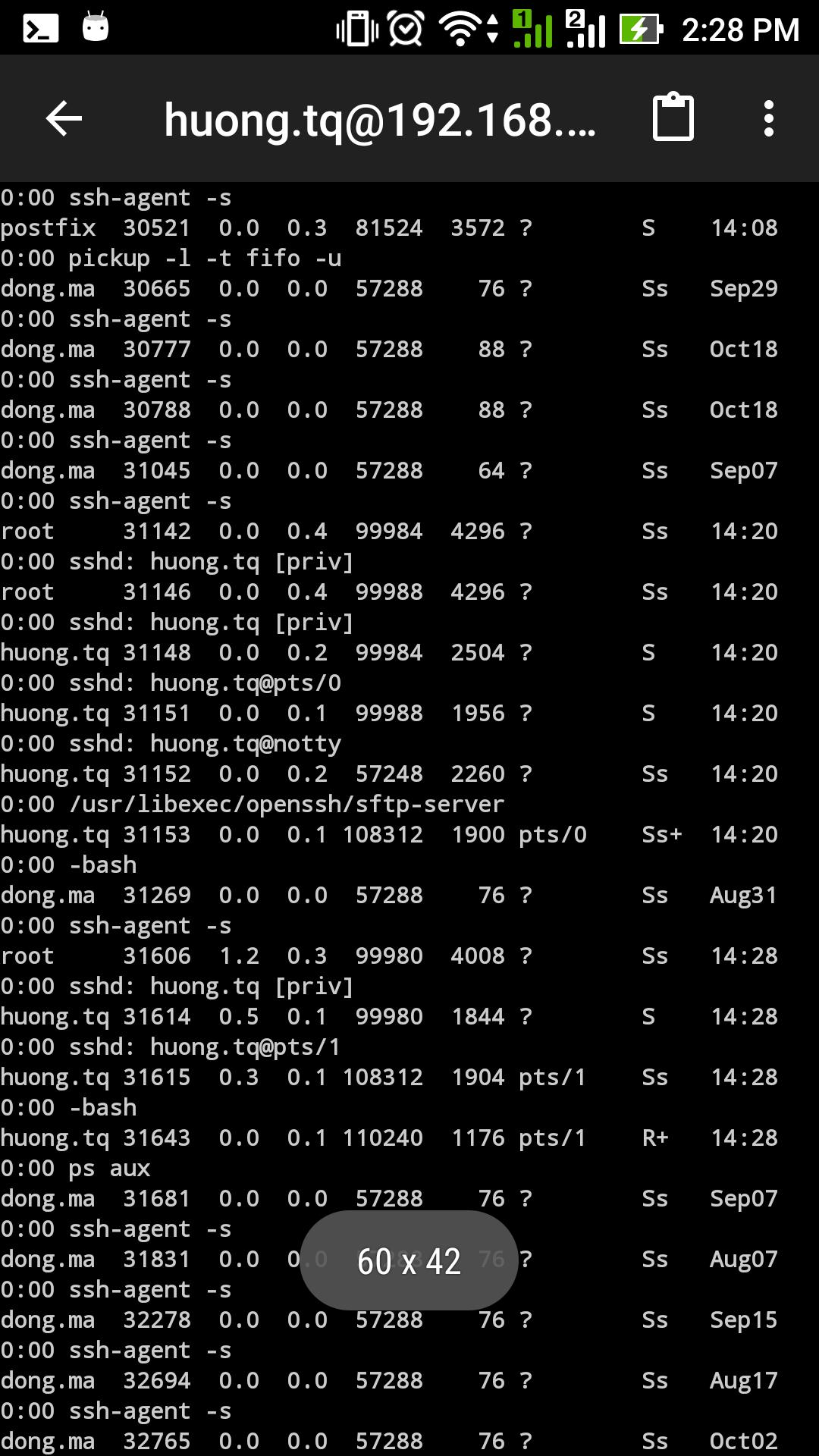
Setting up a secure IoT connection using P2P SSH on Android involves several steps. Follow this guide to ensure a smooth and secure setup process.
Step 1: Install Required Tools
Begin by installing Termux on your Android device. Termux provides a terminal environment that supports SSH and other command-line tools.
Step 2: Configure SSH
Once Termux is installed, configure SSH by generating a key pair. This ensures secure authentication between devices.
Step 3: Establish P2P Connection
Use the SSH client to establish a direct connection between your Android device and the IoT device. Ensure both devices are on the same network for optimal performance.
Enhancing Security Measures
While P2P SSH provides a secure foundation, additional measures can further enhance the security of your IoT connections.
Best Practices for Security
- Regularly Update Software: Keep all devices and software up to date to patch vulnerabilities.
- Use Strong Passwords: Implement complex passwords and consider using two-factor authentication.
- Monitor Activity: Regularly monitor device activity for any suspicious behavior.
Common Issues and Troubleshooting
As with any technology, issues may arise when setting up secure IoT connections. Here are some common problems and their solutions.
Connection Issues
If you encounter connection problems, ensure both devices are on the same network and check firewall settings. Additionally, verify that SSH is properly configured on both devices.
The Future of IoT Security
The future of IoT security lies in advancements such as quantum encryption and blockchain technology. These innovations promise to further enhance the security of IoT devices, making them more resilient to attacks.
Emerging Technologies
- Quantum Encryption: Offers unparalleled security by leveraging the principles of quantum mechanics.
- Blockchain: Provides a decentralized ledger for secure data transactions.
Conclusion and Call to Action
Securing IoT connections is crucial in today's digital landscape. By using P2P SSH on Android, you can establish secure, cost-effective connections that protect your data. This guide has provided a comprehensive overview of the tools and techniques required to achieve this goal.
We encourage you to share your thoughts and experiences in the comments section below. Additionally, explore other articles on our site to deepen your understanding of IoT security and its applications.
Data Sources: This article draws from reputable sources such as SSH.com, Android.com, and WireGuard.com. Always refer to official documentation for the latest information and updates.