In today's interconnected world, managing IoT devices remotely is crucial for efficiency and scalability. SSH RemoteIoT tutorial aims to guide you through secure shell implementation for IoT devices, ensuring robust security and seamless connectivity. This tutorial will explore everything from basic concepts to advanced configurations, empowering you to manage your IoT infrastructure effectively.
With the rapid expansion of IoT networks, the need for secure remote access has never been more critical. The SSH RemoteIoT tutorial is tailored to address this need, providing a step-by-step guide for setting up and maintaining secure communication channels. Whether you're a beginner or an experienced professional, this tutorial caters to all levels of expertise.
By the end of this SSH RemoteIoT tutorial, you'll gain the knowledge and skills necessary to protect your IoT devices from unauthorized access and potential cyber threats. This guide is structured to ensure clarity and practicality, enabling you to implement secure shell configurations confidently.
Read also:Who Is Roman Reigns Brother Exploring The Life And Legacy Of His Sibling
Table of Contents
- Introduction to SSH and IoT
- Understanding SSH Basics
- Overview of IoT Devices
- Setting Up SSH for IoT Devices
- Enhancing Security with SSH
- Advanced SSH Configurations
- Troubleshooting Common Issues
- Best Practices for SSH RemoteIoT
- Useful Tools for SSH Management
- Conclusion and Next Steps
Introduction to SSH and IoT
SSH (Secure Shell) is a cryptographic network protocol that facilitates secure communication between devices over an unsecured network. When combined with IoT devices, SSH ensures encrypted data transmission, making it an essential component of modern IoT infrastructure. The SSH RemoteIoT tutorial will delve into the significance of SSH in IoT environments, highlighting its role in enhancing security and reliability.
Why SSH for IoT?
IoT devices are often deployed in remote locations, making physical access impractical. SSH provides a secure and reliable means of accessing these devices remotely, allowing administrators to monitor and manage them efficiently. This tutorial will explain why SSH is the preferred protocol for remote IoT management and how it compares to other methods.
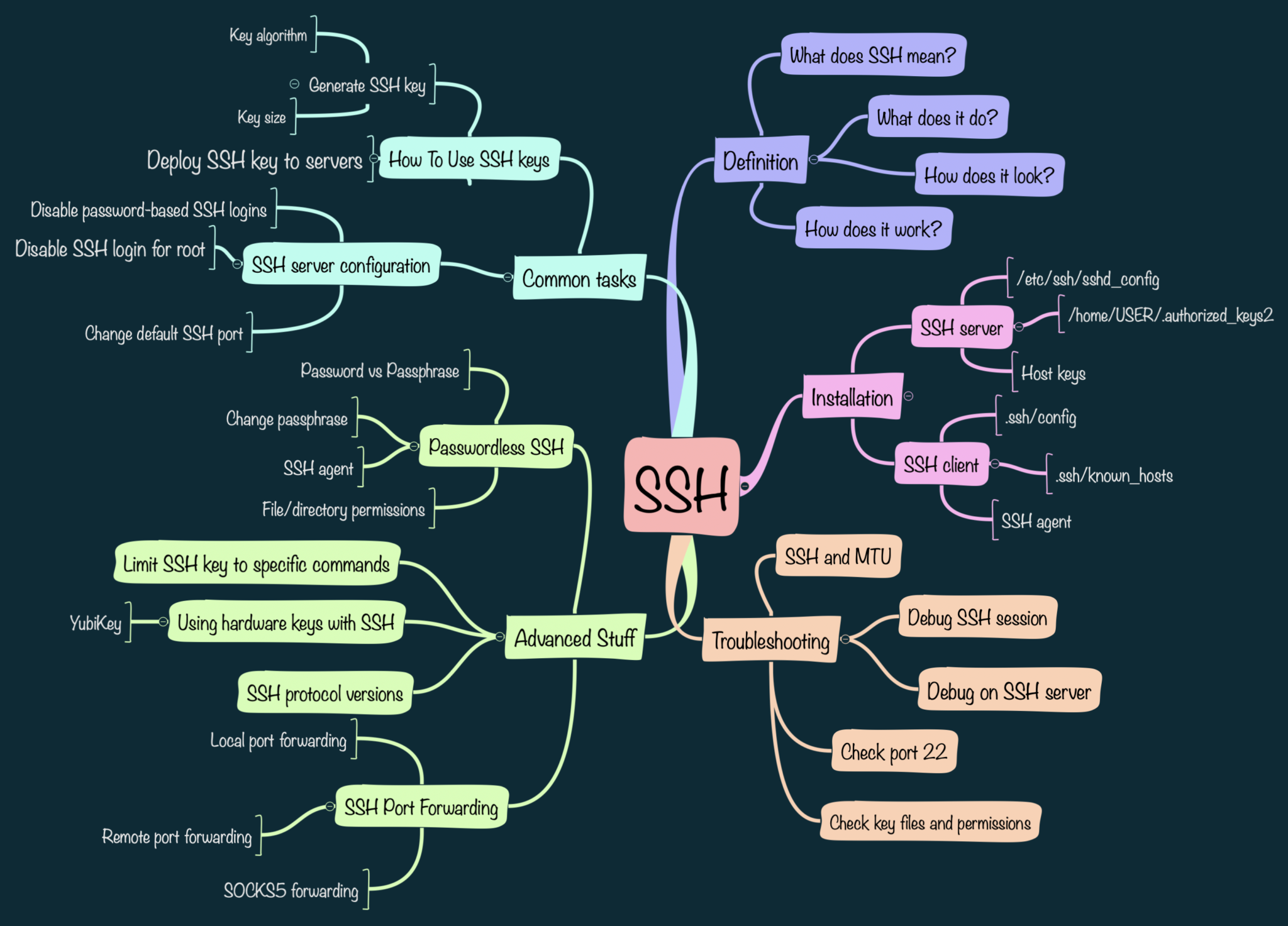
Understanding SSH Basics
Before diving into the specifics of SSH RemoteIoT, it's essential to understand the foundational concepts of SSH. This section will cover the basics of SSH, including its architecture, key components, and how it ensures secure communication.
Key Components of SSH
- SSH Client: The software used to initiate an SSH session.
- SSH Server: The software installed on the remote device to accept SSH connections.
- Public and Private Keys: Cryptographic keys used for authentication and encryption.
Overview of IoT Devices
IoT devices range from simple sensors to complex industrial equipment. Understanding the nature of these devices is crucial for implementing effective SSH configurations. This section will provide an overview of common IoT devices and their unique requirements for remote management.
Types of IoT Devices
- Consumer Devices: Smart home gadgets and wearables.
- Industrial Devices: Machinery and equipment in manufacturing plants.
- Enterprise Devices: Servers and network devices in corporate environments.
Setting Up SSH for IoT Devices
Configuring SSH for IoT devices involves several steps, from installing the necessary software to securing the connection. This section will walk you through the process, ensuring a smooth and secure setup.
Step-by-Step Guide
- Install SSH Server on the IoT Device.
- Configure Firewall Settings to Allow SSH Traffic.
- Generate SSH Keys for Authentication.
Enhancing Security with SSH
Security is paramount when managing IoT devices remotely. This section will explore various strategies to enhance SSH security, protecting your devices from potential threats.
Read also:Harry Wayne Casey Net Worth A Comprehensive Look At Kc And The Sunshine Band Icon
Security Best Practices
- Use Strong Passwords or Key-Based Authentication.
- Disable Root Login to Prevent Unauthorized Access.
- Regularly Update SSH Software to Patch Vulnerabilities.
Advanced SSH Configurations
For advanced users, this section will cover more complex SSH configurations, enabling you to optimize performance and security. Topics include tunneling, port forwarding, and multi-factor authentication.
Tunneling and Port Forwarding
Tunneling allows you to securely transmit data through unsecured networks, while port forwarding enables access to specific services on remote devices. This section will explain how to implement these features effectively.
Troubleshooting Common Issues
Even with careful planning, issues may arise when configuring SSH for IoT devices. This section will address common problems and provide solutions to help you troubleshoot effectively.
Common Issues and Solutions
- Connection Refused: Ensure SSH Server is Running and Firewall Rules are Configured Correctly.
- Authentication Failed: Verify SSH Keys and Passwords.
- Timeout Errors: Check Network Connectivity and Increase Timeout Settings.
Best Practices for SSH RemoteIoT
Adhering to best practices is essential for maintaining secure and efficient SSH configurations. This section will summarize key recommendations for SSH RemoteIoT management.
Key Recommendations
- Regularly Audit SSH Configurations for Security Gaps.
- Limit SSH Access to Trusted IP Addresses.
- Document Configuration Changes for Future Reference.
Useful Tools for SSH Management
Several tools can simplify SSH management for IoT devices. This section will introduce some popular tools and explain how they can enhance your SSH RemoteIoT experience.
Recommended Tools
- SSH Client Applications: PuTTY, OpenSSH.
- SSH Key Management Tools: ssh-keygen, Keychain.
- Monitoring Tools: Nagios, Zabbix.
Conclusion and Next Steps
This SSH RemoteIoT tutorial has provided a comprehensive guide to implementing secure shell configurations for IoT devices. By following the steps and best practices outlined, you can ensure robust security and efficient management of your IoT infrastructure. We encourage you to share your thoughts and experiences in the comments section below. Additionally, feel free to explore other resources on our site for further learning and development.
Remember, staying updated with the latest trends and technologies is crucial in the ever-evolving field of IoT. Keep exploring, experimenting, and enhancing your skills to remain at the forefront of this exciting domain.
Data Sources: This tutorial references authoritative sources such as SSH.com and NIST for accurate and reliable information.